Keystroke Dynamics Uses Two Unique Typing Variables
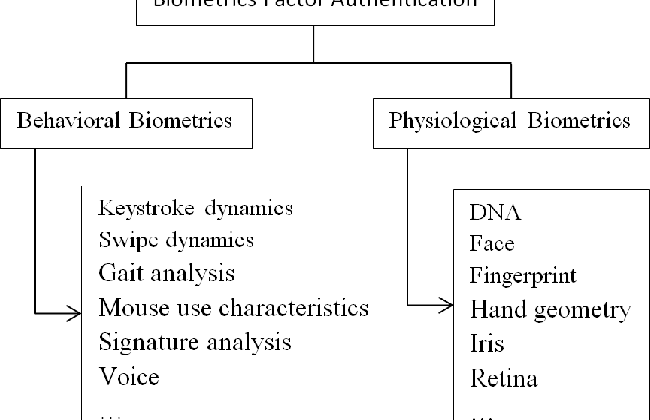
Keystroke dynamics are one of behavioral biometrics and look at the way a person types at a keyboard. Keystroke dynamics uses two unique typing variables.
A Keystroke Biometric System For Long Text Input Document Gale Academic Onefile
Keystroke dynamics uses two unique typing variables.

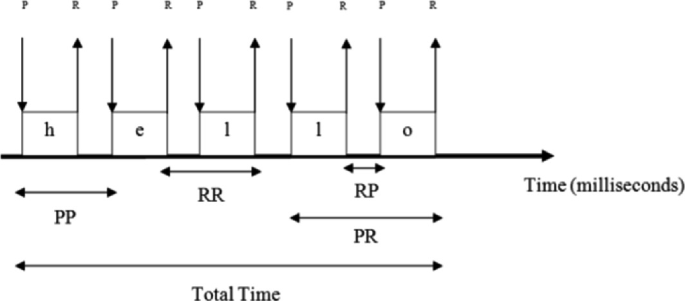
. Dwell time which is the amount of time you hold down a particular key and flight time which is the amount of time it takes a person to move between keys. Solutions for Chapter 10 Problem 9RQ. One type of behavioral biometrics is keystroke dynamics which attempts to recognize a users unique typing rhythm.
Vibration information may be used to create a pattern for future use in both identification and authentication tasks. User Authentication Using Keystroke Dynamics. A rarely talked about field of research known as keystroke dynamics involves identifying individuals based on how they type on a keyboard.
View Chapter 11- Quiz Gradeddocx from CTS 1120 at Miami Dade College Miami. Keystroke dynamics is the study of whether people can be distinguished by their typing rhythms much like handwriting is used to identify the author of a written text. In this lab well run an application tha.
Diagraph comes under Press-to-Press category. Keystrokes are separated into static and dynamic typing which are used to help distinguish between authorized and unauthorized users. Answer to Keystroke dynamics is an example of _____ biometrics.
Keystroke dynamics is a behavioral biometric this means that the biometric factor is something you do. The calculation is done using the famous coupon collector problem. When used in a logical access control the keystroke dynamics process uses different.
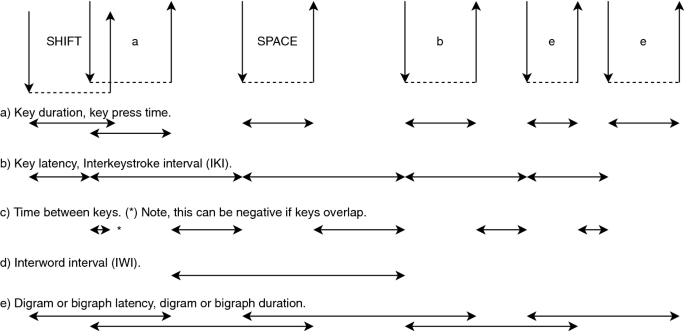
In keystroke dynamics measures two variables. And others published Keystroke Dynamics for User Authentication and Identification by using Typing Rhythm Find. Data needed to analyse keystroke dynamics is obtained by keystroke logging.
Behavioral Biometrics QUESTION TYPE. Digraph two letters or tri-graph three letters can also be extracted. Factors are also expected to make typing characteristics unique as per person.
Unlike other biometrics like IRIS face fingerprints etc which need special hardware infrastructure. In addition some studies showed that keystroke dynamics holds better performance when using simple passwords than more complicated ones. A long time ago in the minds of many tinkerers an idea about how everyone has an inherently unique style of typing was born.
True False HAS VARIABLES. Already during the second world war a technique known as The Fist of the. Specifically keyboard dynamics measures two distinct variables.
Keystroke dynamics is considered seamless and transparent. Keystroke dynamics verification in a browser using JavaScript. Keystroke signature fuses the simplicity of passwords with increased reliability from biometrics.
Asked Feb 14 2019 in Computer Science Information Technology by Dannylee Answer the following statement true T or false F. Up to 10 cash back Keyboard dynamics are the characteristics of typing or rhythmic patterns of sequences of keystrokes on a keyboard. True Hash algorithms like MD5 and SHA are considered secure for creating digests because these hashing algorithms are designed to create a digest as strong as possible.
Keystroke dynamics does not protect against replay attacks. You know uniqueness is very hard to prove or produce in Computer Science. It was found that a hybrid sum-of-products network gave the.
Keystroke dynamics or typing biometrics refers to the automated method of identifying or confirming the identity of an individual based on the manner and the rhythm of typing on a keyboard. Using Keystroke dynamics authentication technology can be secured by password from. One possible solution that has gained notable attention is keystroke dynamics which deals with verifying the users identity based on the unique way people type on the keyboard.
Normally all that is retained when. Your unique typing rhythm can reveal your identity. Get solutions Get solutions Get solutions done loading Looking for.
If the user keeps a simple password he remembers it more easily and administrators lost less time by giving new passwords. Keystroke dynamics uses two unique typing variables. The unique typing patterns of users can be used as a signature to identify genuine users from imposters.
The attacker will not be able to replay or semi-replay informations. Quiz Graded Attempt Score 100 out of 100 points Question 1. Although this topic has been researched for several decades 1 in recent years it has gained popularity in both academia and industry due to its ability to detect.
For this reason keystroke dynamics has been used for security purposes such as user authentication 21 and user identi cation 22 to di erentiate between two. The idea behind keystroke dynamics. Its getting better and also easier for anyone to implement.
Download Citation On Jun 17 2016 Rohit A. First is dwell time which is the period of time you hold down a particular key and second is flight time which is the period of time you release those keys. We suggest a more secure protocol for keystroke dynamics authentication.
The United States conducted studies establishing that typing patterns contain unique characteristics that can be identified. Background Early telegraph operators realized that they could identify other operators through the. Keystroke dynamics is an example of _____ biometricsa.
The initial use of ANNs was to aid in user identification using keystroke dynamics Obaidat and Macchairolo 1993 1994 and several of the first wave of studies to implement such a neural network approach simply used users keystroke latencies as the basis for discrimination. Possible applications include acting as an electronic fingerprint or in an access-control mechanism.
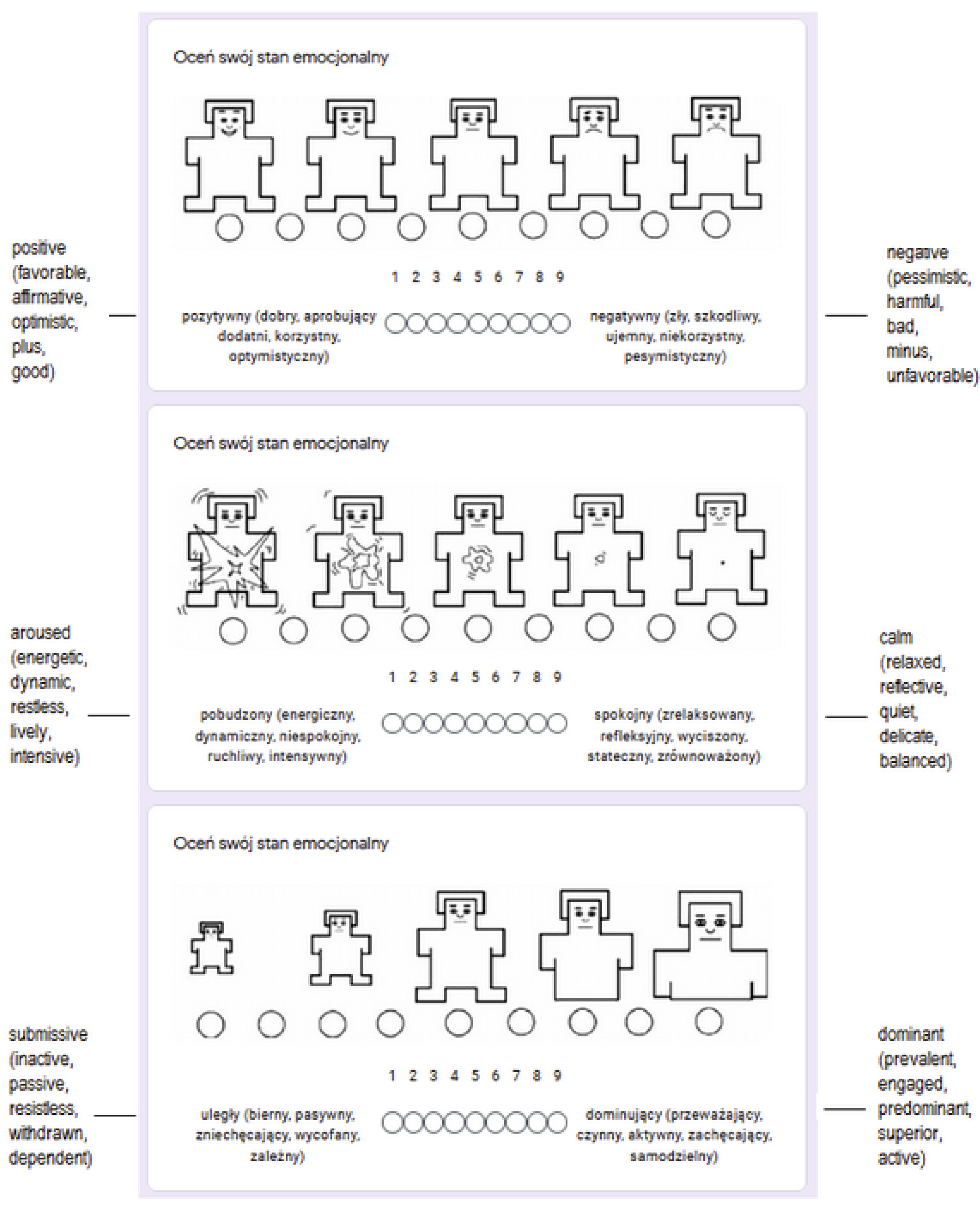
Sensors Free Full Text Keystroke Dynamics Patterns While Writing Positive And Negative Opinions Html

Security Guide To Network Security Fundamentals Fifth Edition Ppt Download

Scope Of Php In Future And Mncs Hiring Php Developers Php Tutorial Web Development Development
Keystroke Biometrics In The Encrypted Domain A First Study On Search Suggestion Functions Of Web Search Engines Springerlink

Multimodal Mobile Keystroke Dynamics Biometrics Combining Fixed And Variable Passwords Alshanketi 2019 Security And Privacy Wiley Online Library

Multimodal Mobile Keystroke Dynamics Biometrics Combining Fixed And Variable Passwords Alshanketi 2019 Security And Privacy Wiley Online Library
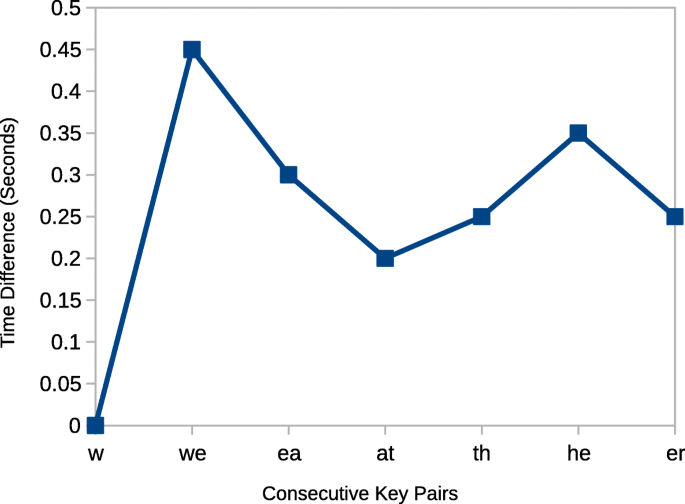
Understanding The Keystroke Log The Effect Of Writing Task On Keystroke Features Springerlink

Security Guide To Network Security Fundamentals Fourth Edition Ppt Video Online Download

Sensors Free Full Text Keystroke Dynamics Patterns While Writing Positive And Negative Opinions Html
Behavioral Biometrics Scheme With Keystroke And Swipe Dynamics For User Authentication On Mobile Platform Semantic Scholar

Sensors Free Full Text Keystroke Dynamics Patterns While Writing Positive And Negative Opinions Html

Wpm Versus Keystrokes Per Character With 95 Confidence Region Typists Download Scientific Diagram

Multimodal Mobile Keystroke Dynamics Biometrics Combining Fixed And Variable Passwords Alshanketi 2019 Security And Privacy Wiley Online Library
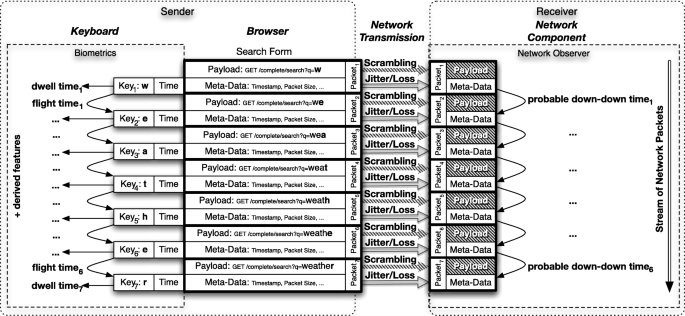
Keystroke Biometrics In The Encrypted Domain A First Study On Search Suggestion Functions Of Web Search Engines Springerlink

Multimodal Mobile Keystroke Dynamics Biometrics Combining Fixed And Variable Passwords Alshanketi 2019 Security And Privacy Wiley Online Library

Multimodal Mobile Keystroke Dynamics Biometrics Combining Fixed And Variable Passwords Alshanketi 2019 Security And Privacy Wiley Online Library

Pdf User Authentication Using Keystroke Dynamics For Cellular Phones
Comments
Post a Comment